65.3.1 NAT Traversal
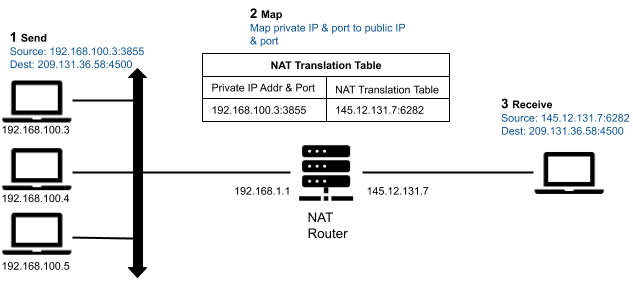
In WAN environments, applications running behind a NAT-enabled router typically need to communicate with applications running behind a different NAT-enabled router. NAT (Network Address Translation) is a method of remapping one private IP address and port into a public IP address and port by modifying the IP address and port information in the IP header of the packets while they are in transit across a NAT-enabled router. The technique has become a popular and essential tool in conserving the IPv4 global address space in the face of IPv4 address exhaustion. Many applications with individual private IP addresses can utilize a NAT-enabled router to communicate with external applications using a single public IP address.
Figure 65.1: NAT Traversal
Real-Time WAN Transport in combination with Cloud Discovery Service will enable communications between Connext applications running between different kinds of NATs. For information on the various NAT kinds, please see the following sections.
65.3.2 NAT Kinds
There are four kinds of NATs:
65.3.2.1 Full-Cone NAT (or One-to-One NAT)
A full-cone NAT, also known as a one-to-one NAT, has the following characteristics:
- Once an internal address (iAddr:iPort) is mapped to an external address (eAddr:ePort) by the NAT router, any packets from (iAddr:iPort) are sent through (eAddr:ePort).
- Any external host can send packets to (iAddr:iPort) by sending packets to (eAddr:ePort), regardless of the external host address/port (dAddr:dPort) used to send the packets.
Figure 65.2: Full-Cone NAT
65.3.2.2 Address-Restricted-Cone NAT
- Once an internal address (iAddr:iPort) is mapped to an external address (eAddr:ePort) by the NAT router, any packets from (iAddr:iPort) are sent through eAddr:ePort.
- An external host (dAddr:any) can send packets to (iAddr:iPort) by sending packets to (eAddr:ePort) only if (iAddr:iPort) has previously sent a packet to (dAddr:any). "Any" means the port number doesn't matter.
65.3.2.3 Port-Restricted Cone NAT
This NAT is similar to an address-restricted cone NAT, but the restriction also includes port numbers.
- Once an internal address (iAddr:iPort) is mapped to an external address (eAddr:ePort) by the NAT router, any packets from (iAddr:iPort) are sent through (eAddr:ePort).
- An external host (dAddr:dPort) can send packets to (iAddr:iPort) by sending packets to (eAddr:ePort) only if (iAddr:iPort) has previously sent a packet to (dAddr:dPort).
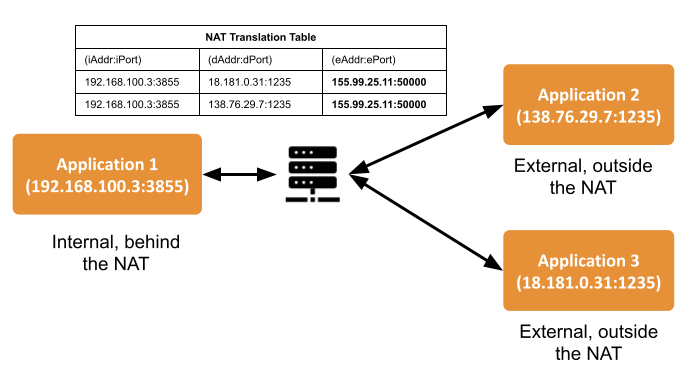
65.3.2.4 Symmetric NAT
- Each request from the same internal IP address and port (iAddr:iPort) to a specific destination IP address and port (dAddr:dPort) is mapped by the NAT router to a unique external source IP address and port (eAddr:ePort). If the same internal host sends a packet even with the same source address and port but to a different destination, a different mapping is used.
- Only an external host that receives a packet from an internal host can send a packet back.
Figure 65.3: Symmetric NAT

65.3.3 Identifying the NAT Type
There are multiple third-party utilities that you can download to find out the NAT type. One example is natat (https://github.com/songjiayang/natat).
> ./natat
2020/11/21 11:10:52 start stun server ping...
2020/11/21 11:10:53 stun.l.google.com:19302 mapped: 0.0.0.0:3489 -> 99.35.17.233:3489
2020/11/21 11:10:53 stun1.l.google.com:19302 mapped: 0.0.0.0:3489 -> 99.35.17.233:3489
2020/11/21 11:10:53 start NAT type assert...
2020/11/21 11:10:53 It's Cone NAT
65.3.4 NAT Bindings
Applications behind a NAT cannot receive data from applications outside the NAT unless they open a UDP NAT binding (or UDP hole) with each one of the public IP transport addresses associated with the applications running outside the NAT.
A NAT binding creates a mapping between a private IP transport address (iAddr:iPort) and a public IP transport address (eAddr:ePort) for a given set of destination IP transport addresses. There are two kinds of bindings:
- Static bindings (also known as port forwarding): You can set the configuration of a NAT-enabled router to map (iAddr:iPort) to (eAddr:ePort) (see Figure 65.4: Open a Static Binding in a NAT-Enabled Router) for all destination addresses. These bindings allow incoming traffic from any external IP transport address.
- Dynamic bindings: The bindings are opened dynamically when the application running inside the NAT sends a message to a destination IP transport address outside the NAT. The behavior of the dynamic bindings depends on the type of NAT (see 65.3.2 NAT Kinds). Unlike static bindings, dynamic bindings can expire if there is no outgoing traffic (see 65.3.5 NAT Bindings Expiration).
Figure 65.4: Open a Static Binding in a NAT-Enabled Router

65.3.5 NAT Bindings Expiration
Real-Time WAN Transport will be able to establish new NAT bindings if the old bindings are closed by the NAT-enabled router without any user intervention. In addition, Real-Time WAN Transport provides a builtin Ping mechanism to keep the NAT bindings open at all times. This capability eliminates the latency penalty that is introduced during the process of establishing a new NAT binding.
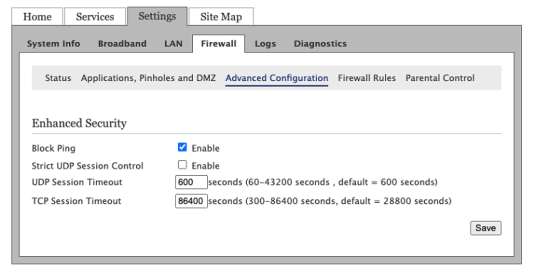
For security purposes, in the absence of outbound traffic, the NAT binding from an internal address (iAddr:iPort) to an external address (eAddr:ePort) usually expires after periods of time in the range of tens of seconds to a few minutes. When it expires, the NAT binding is removed and it closes. The expiration time can usually be configured (see Figure 65.5: Session Timeout).
65.3.6 NAT Hairpinning
Real-Time WAN Transport does not require support for NAT hairpinning and can be used in combination with the builtin UDPv4 transport in a DomainParticipant to support both communication with DomainParticipants within the same LAN and communication with DomainParticipants in a WAN simultaneously.
In network computing, hairpinning (or NAT loopback) refers to communication between two hosts behind the same NAT router using their mapped external address (eAddr:ePort). Because not all NAT routers support this communication configuration, usually applications must be designed to be aware of it.