19. DDS Security Data Visualization with RTI Administration Console
RTI Admin Console is compatible with Security Plugins. Configuring security in
Admin Console will allow you to visualize and troubleshoot your DDS Secure
system. The security configuration is under Preferences >
Security. There, you can secure Admin Console’s DomainParticipants by checking
the Enable Security for specified Domains checkbox. The security
preferences will only apply to the domains listed in the
Domain Filter field. Note that a * in this field will apply
security to all domains; you can also use patterns like 2,3 or
8,9-12,23.
After setting the Domain Filter to the desired domains where you want to visualize your DDS Secure system, you have to set the security artifacts that Admin Console’s DomainParticipants will use, as shown in Table 19.1, Table 19.2, Table 19.3, Table 19.4.
Note
As a prerequisite for using security in Admin Console, you need to install the Security Plugins. For this, you can follow the instructions in the RTI Security Plugins Installation Guide.
Figure 19.1 is an example of the values to configure Admin Console to work with the “Security::SecureAllowAll” profile of Shapes Demo:
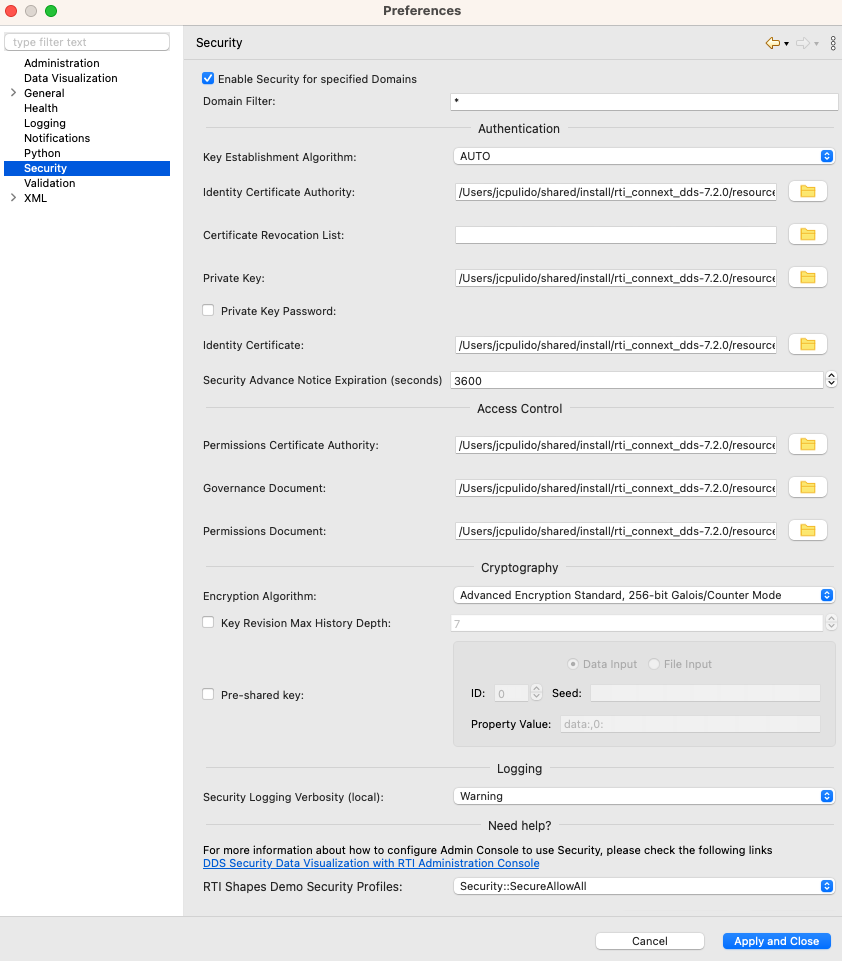
Figure 19.1 Security Panel in Admin Console’s Preferences
The following tables describe the purpose of each field.
Note
If you are using Admin Console 5.3.x, make sure to click the Apply button. This is critical because the settings won’t be applied if you just click OK.
Field |
Description |
|---|---|
Key Establishment Algorithm |
Required The algorithm used to establish a Shared Secret during authentication, as
defined by the For details, see Table 4.2. |
Identity Certificate Authority |
Required Provides Admin Console’s DomainParticipants with the Identity CA, as defined by the
For details, see Table 4.1. |
Certificate Revocation List |
Optional The Identity CA can maintain a certificate revocation list (CRL) with information about digital certificates that have been revoked before their scheduled expiration date and should no longer be trusted. With this field you can provide the CRL to the Admin Console’s DomainParticipants, as
defined by the For details, see Table 4.2. |
Private Key |
Required Provides Admin Console’s DomainParticipants with a Private Key, as defined by the
For details, see Table 4.1. For details, see Table 4.1. |
Private Key Password |
Only required if the Private Key is encrypted The password used to decrypt the Private Key. This field is interpreted
as the Base64 encoding of the symmetric key that will be used to decrypt
the Private Key, as defined by the If the password is wrong, Admin Console will fail to create the secure participants and will report multiple errors in the Console Log. |
Identity Certificate |
Required Provides Admin Console’s DomainParticipants with an Identity Certificate, as defined by the
|
Security Advance Notice Expiration (seconds) |
Required Controls how much time in advance to notify the user when a local DomainParticipant’s
security artifacts (Identity Certificate or Permissions Document) is about to
expire. For more information, read the documentation on the
|
Field |
Description |
|---|---|
Permissions Certificate Authority |
Required Provides Admin Console’s DomainParticipants with the Permissions CA, as defined by the
For details, see Table 5.3. |
Governance Document |
Required Provides Admin Console’s DomainParticipants with the Governance Document, as defined by
the For details, see Table 5.3. |
Permissions Document |
Required Provides Admin Console’s DomainParticipants with the Permissions Document, as defined by
the For details, see Table 5.3. |
Field |
Description |
|---|---|
Encryption Algorithm |
Required The algorithm that the Sender uses for the encryption transformation, as
defined by the For details, see Table 6.8. |
Key Revision Max History Depth |
Optional Number of key revisions used to encode samples in the DataWriter’s queues, as
defined by the |
Pre-shared secret passphrase |
Only required if pre-shared key protection is enabled Seed used to derive the pre-shared key (in combination with publicly
available data). The key is used for encoding and decoding RTPS messages.
It is only effective in Builtin Security Plugins if the Governance Document configures
the |
Field |
Description |
|---|---|
Security Logging Verbosity (local) |
Required The logging verbosity level, as defined by the
For details, see Table 7.2. |
19.1. RTI Admin Console and the Lightweight Builtin Security Plugins
Admin Console loads the Builtin Security Plugins library (nddssecurity) when you check Enable Security for specified Domains in the Security panel of Admin Console’s preferences.
Currently, there is no Graphical User Interface option to load the Lightweight Builtin Security Plugins library (nddslightweightsecurity) instead of the Builtin Security Plugins. However, you can still use Admin Console in combination with Lightweight Builtin Security Plugins if you set a custom QoS profile that loads the Lightweight Builtin Security Plugins library. To do so, follow the instructions in Using your own QoS profile in RTI Admin Console from our Knowledge Base. A simple QoS file would look like:
<?xml version="1.0"?> <dds xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:noNamespaceSchemaLocation="https://community.rti.com/schema/6.1.1/rti_dds_profiles.xsd"> <qos_library name="ExampleAdminConsole"> <qos_profile name="BaseProfile" base_name="BuiltinQosLib::Generic.Security"> <!-- Copy here the contents of the BaseProfile that you can find in $NDDSHOME/resource/xml/RTI_ADMIN_CONSOLE_EXAMPLE_PROFILE.xml It is important that now the profile inherits from "BuiltinQosLib::Generic.Security". --> </qos_profile> <qos_profile name="Default" base_name="ExampleAdminConsole::BaseProfile"> <!-- Copy here the contents of the Default that you can find in $NDDSHOME/resource/xml/RTI_ADMIN_CONSOLE_EXAMPLE_PROFILE.xml Nothing changes with respect to RTI_ADMIN_CONSOLE_EXAMPLE_PROFILE.xml. --> </qos_profile> <!-- Load the |LIGHT_SP_BUILTIN_HEADING| and set the pre-shared key seed. You can configure additional QoS values here. --> <qos_profile name="PreSharedKey" base_name="ExampleAdminConsole::Default"> <domain_participant_qos> <property> <value> <element> <name>com.rti.serv.secure.library</name> <value>nddslightweightsecurity</value> </element> <element> <name>dds.sec.crypto.rtps_psk_secret_passphrase</name> <value>UseYourOwnSecretSeed</value> </element> </value> </property> </domain_participant_qos> </qos_profile> </qos_library> </dds>